What you cannot see cannot hurt you. Right?
When I talk with clients about cyber security, I ask them what a great cyber security practice looks like from their point of view. The easy answer is that we stop every attack from happening. Ideally without us having to lift a finger. This allows the typically overworked and understaffed infosec teams a life outside of a constant feeling of playing catch up when something happens. We would all love to put some magical technology that just simply stops every threat. That is the dream.
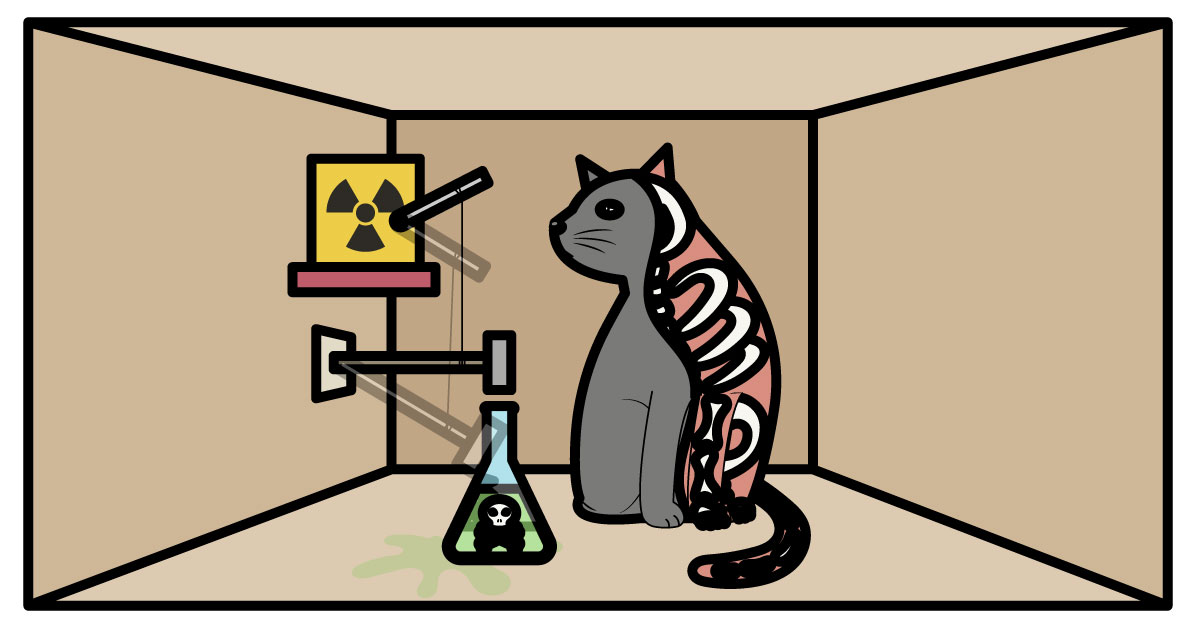
The reality is typically one of two things. One, we put in place some technologies in our security stack that blocks and prevents harmful stuff from happening. We then go to bed at night feeling like we did everything we could to secure our environment. Fingers crossed. Sometimes we are so confident in our abilities to purchase, deploy, and manage the best solutions that we get a false sense of security. I mean if you cannot see it then does it really exist? Sometimes we approach security like Schrödinger's cat. It is only real if it is observed. If it is not observed does it really exist? The problem with this mindset is that someone will eventually see it. More likely someone outside of your organization. Once the Cat’s out of the bag (or box if you like the Schrödinger's cat reference) then it does become real. And if this happens then you lose control of how it is managed. You lose your ability to proactively respond and dictate the narrative. Seeing is believing and therefore you not only need to see what you have stopped but you also need to see what you may not have stopped.
In the 2021 Mandiant M-Trends report, they talk about how 59% of the security incidents were initially detected by the organization themselves. This is a significant increase from previous years. Most of the increase is due to two factors. One, there has been an increasing trend towards compromises via ransomware. Ransomware, unlike more traditional attacks, does not want to be hidden. It will let the organization know it is there before some outside party discovers it. Second, would be the increased efficacy of detection technology. We have seen increased features, functions, and intel inside such products as network security and endpoint security. As many of these products have not only increased their ability to detect known and signature “evil” but they have also moved to a more behavior-based detection. In many cases, this behavior-based detection can bring some additional blocking and prevention, but it also gives more visibility into how these vector points are exploited. Another area of improvement has been in the investments these products have made with Intel. This is usually acquired in two methods. The vendors are purchasing and integrating intel threat feeds or investing in their own IR teams. Some vendors even do both. This increases the vendor's IOC (indicators of compromise) repository. IOC’s go beyond detection and prevention of known and signature-based attributes, but it creates visibility into “methodology” attacks. Methodology is how an attacker leverages both legitimate tools (think PowerShell) and attacker tools like that establish a backdoor like Beacon or Empire into the system. Many of these tools can be modified to bypass signature detection and prevention. Once in the attacker covers their trail and quickly moves to other tools and commands. Never staying long with how they established the backdoor.
In summary. If you cannot see it, that does not mean it is not there.
VLCM works with our customers to provide consultative services to identify areas their customers have little to no visibility in. With a security portfolio of over 110 security vendors, we can assist in giving our customers more visibility into what is happening in their environments. Helping bolster the customer's security practice and helping to decrease their risk profile.
If you are interested in learning more about how we can help, please contact me or someone on our security teams at sales@vlcm.com
Jamie Maxfield
Sr. Cyber Security Engineer and Director of Technical Sales
LinkedIn: https://www.linkedin.com/in/jamie-maxfield-28765a3/
